On August 18, 1913, a roulette wheel in Monte Carlo came up black 26 times in a row. The odds of that happening are approximately 136,823,183 to 1.
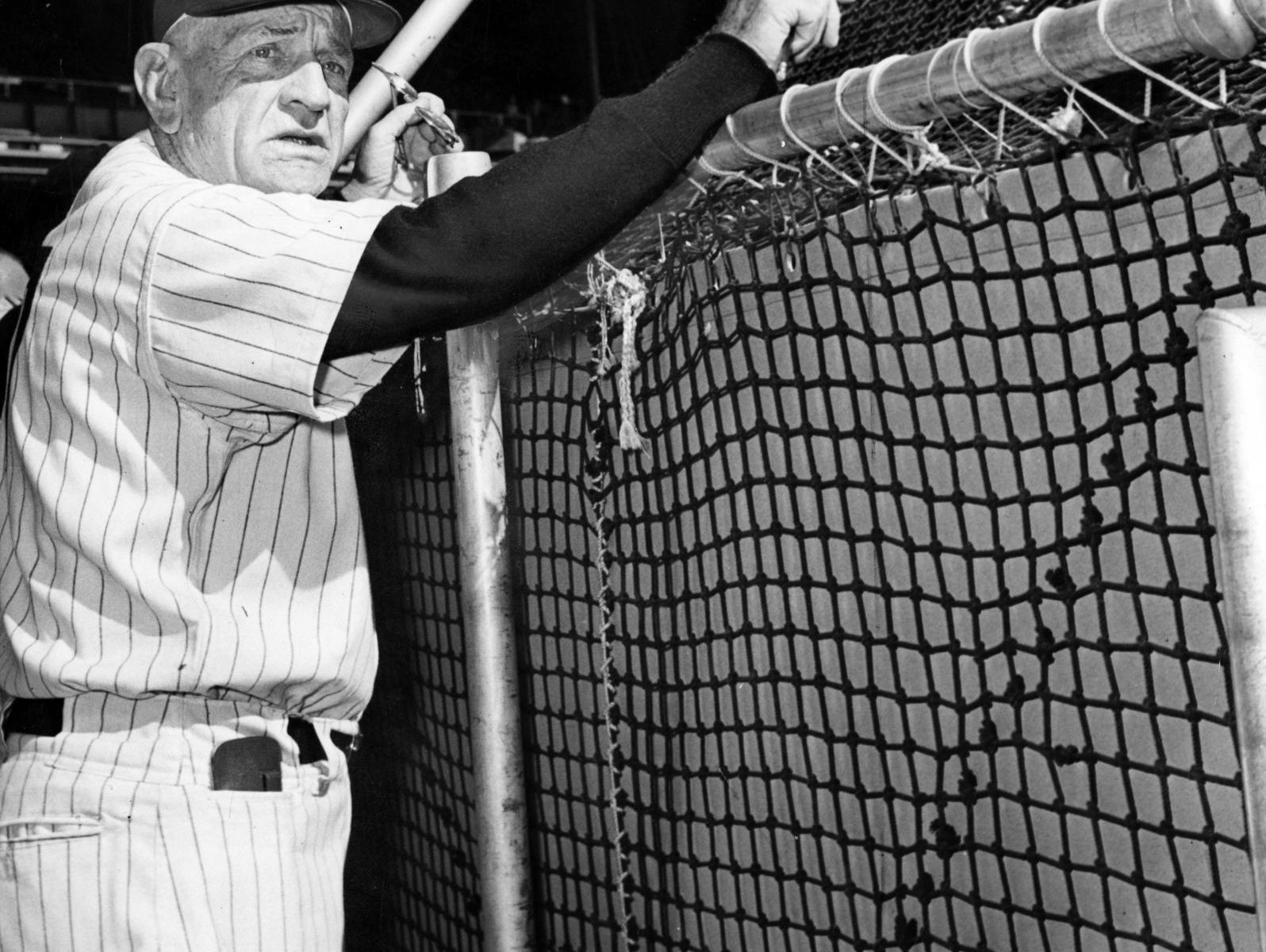
Casey Stengel
“The secret of managing is to keep the guys who hate you away from the guys who are undecided.”
What Are the Odds?
What incredibly unlikely event took place in Monte Carlo on August 18, 1913?
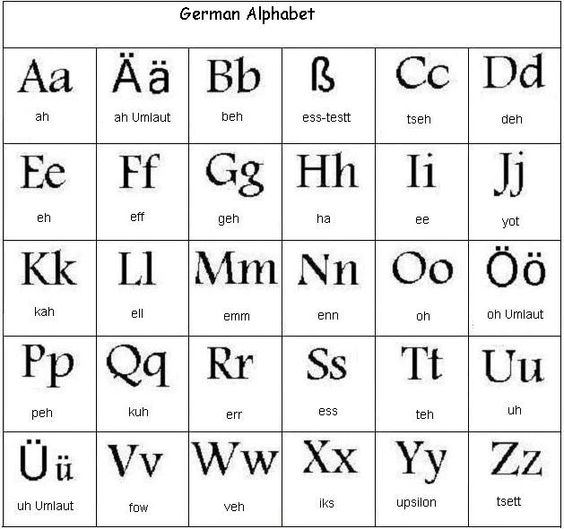
More Letters Than . . .
There are 30 letters in the German alphabet!
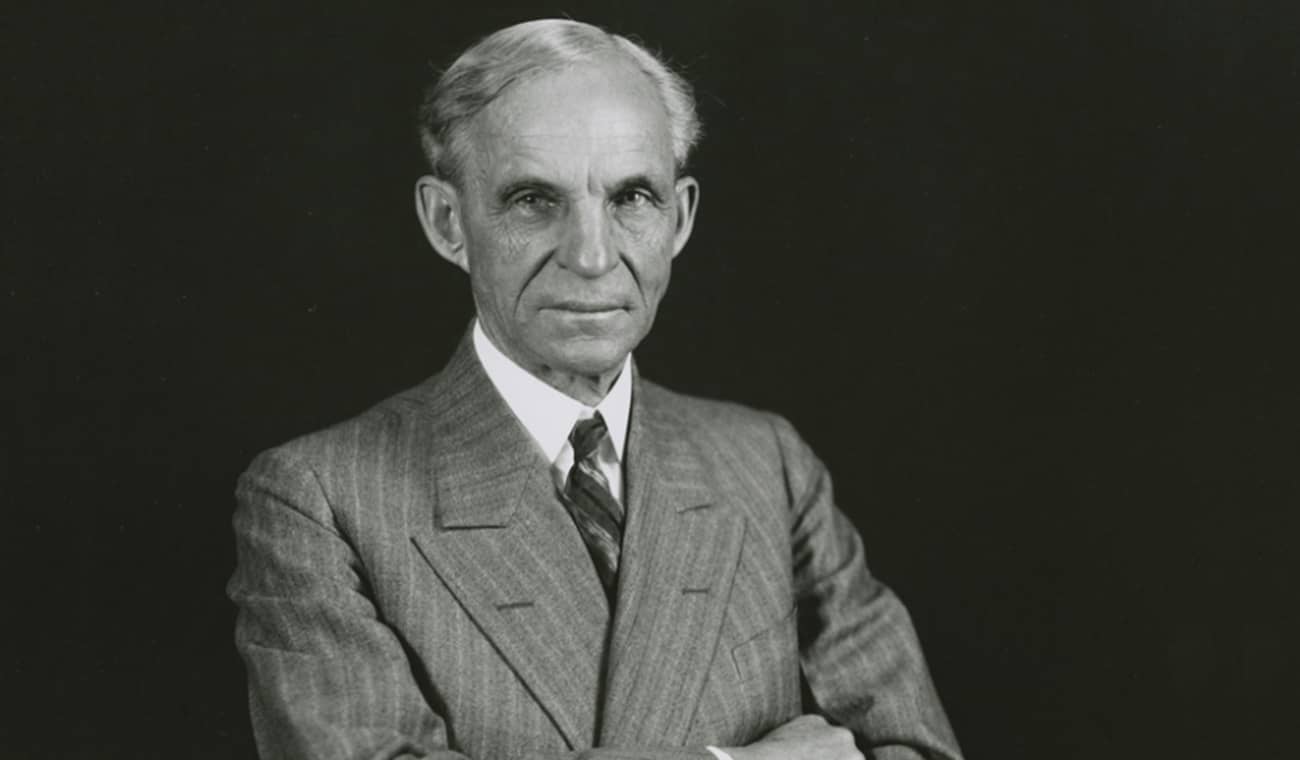
Henry Ford
“The two most important things in any company do not appear in its balance sheet: its reputation and its people.”
A, B, C, D . . .
How many letters are there in the German alphabet?
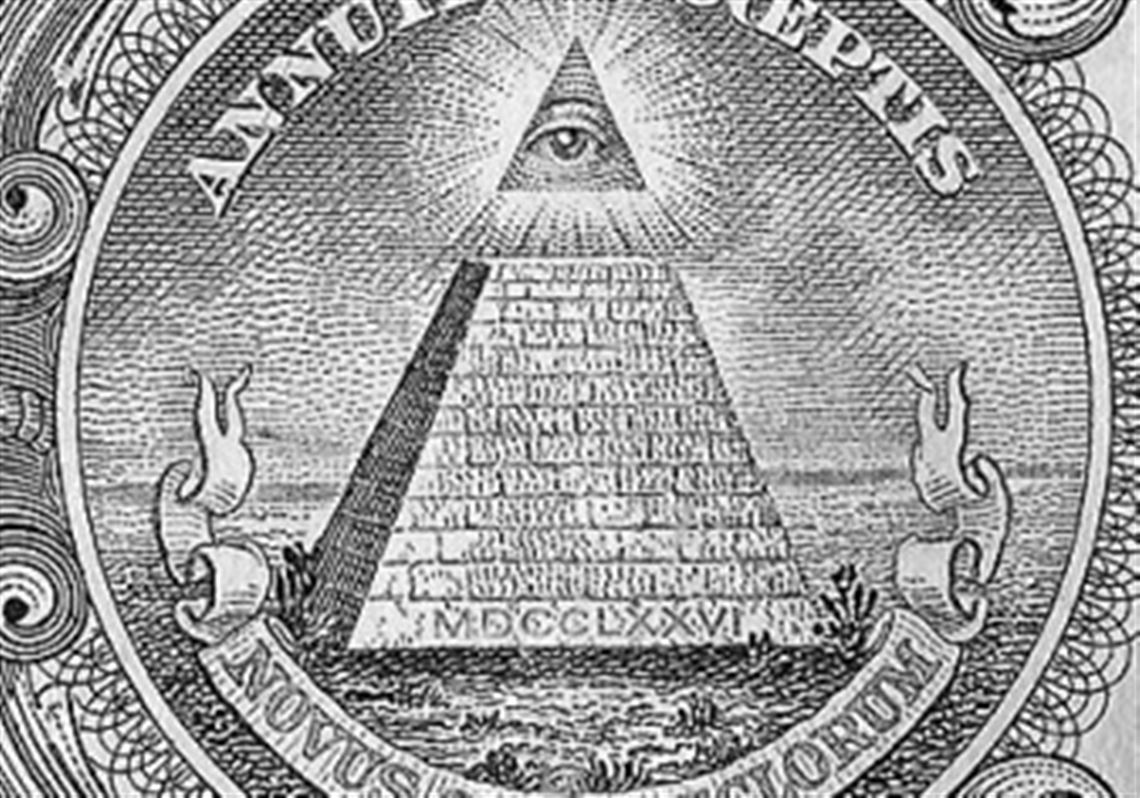
Symbol Minded
Both K and M are symbols for one thousand (1000)!
Joseph E. Levine
“You can fool all the people all the time if the advertising is right and the budget is big enough.”
Robert Langdon Would Know
What do the letters K and M have in common?
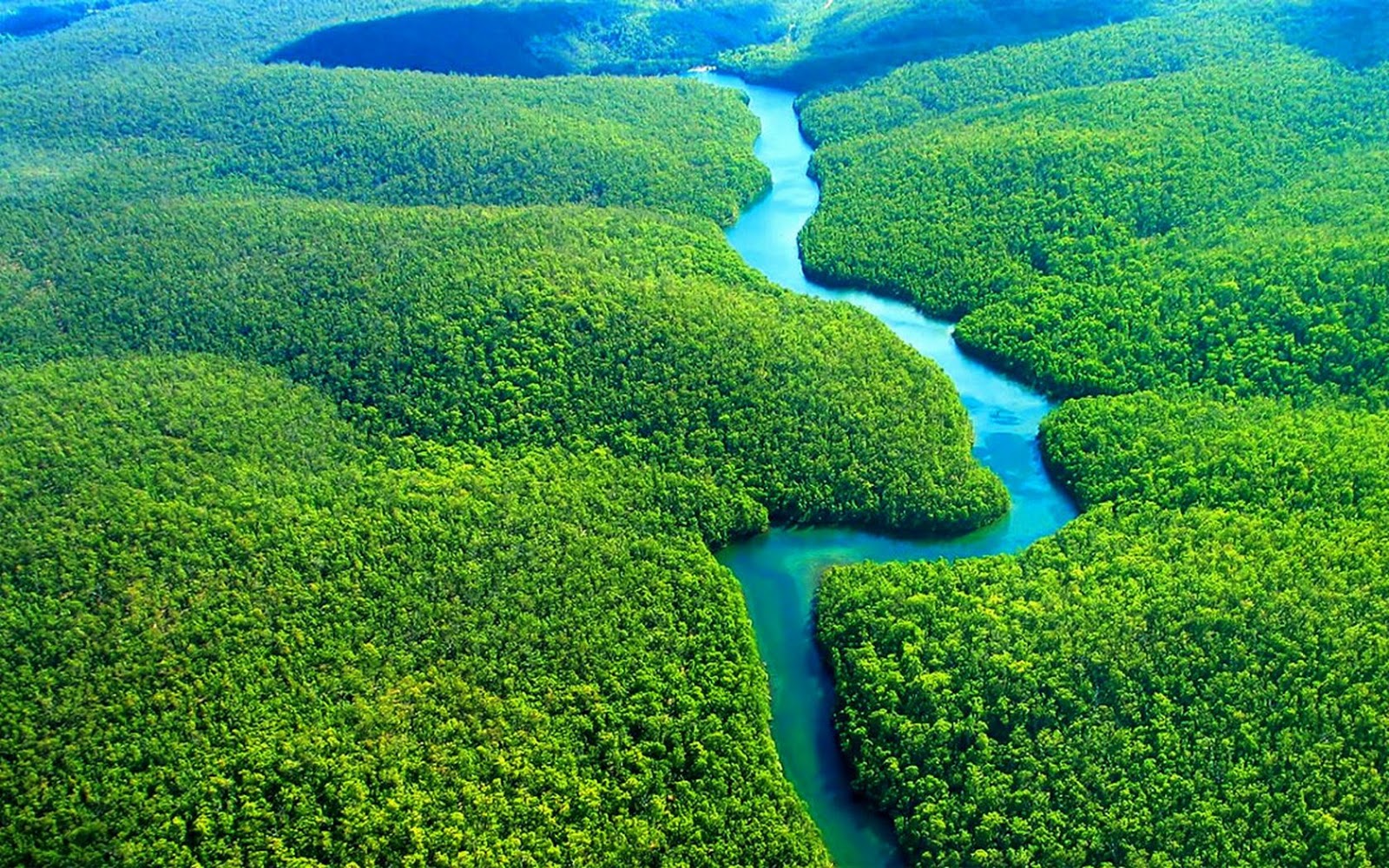
The Amazing Amazon
The worlds largest supply of fresh water is estimated to be found in Brazil, with Canada and Russia next in line (or streaming, in today’s world)!