“Sometimes the questions are complicated and the answers are simple.”
Nobel and Abel
Who is the only person to have won both the Nobel Prize and the Abel Prize?
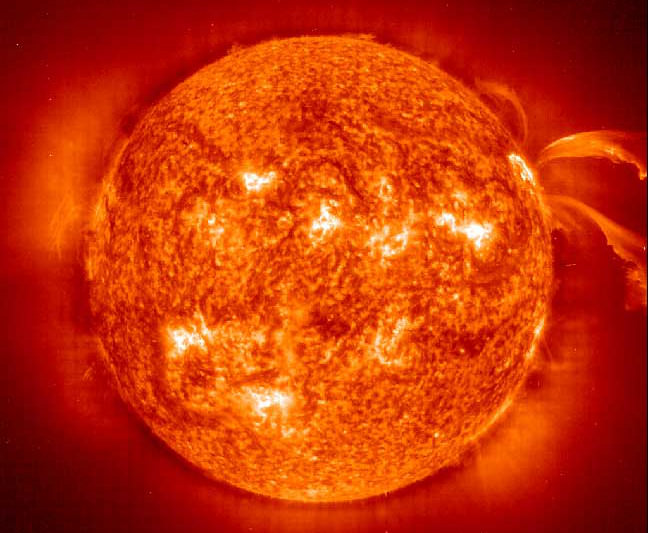
The Sun Gets Around
By initially observing the movement of sunspots, scientist concluded that the Sun does rotate, but because the Sun is made up of gaseous elements and is not solid, the rotation is uneven. The rotations at the equator is about once in a little over 25 days, but at the poles about 36 days and varying in between. The Sun is also tilted on its axis of rotation (relative to the Earth and our point of view). But never look directly at the Sun without special protection for your eyes.
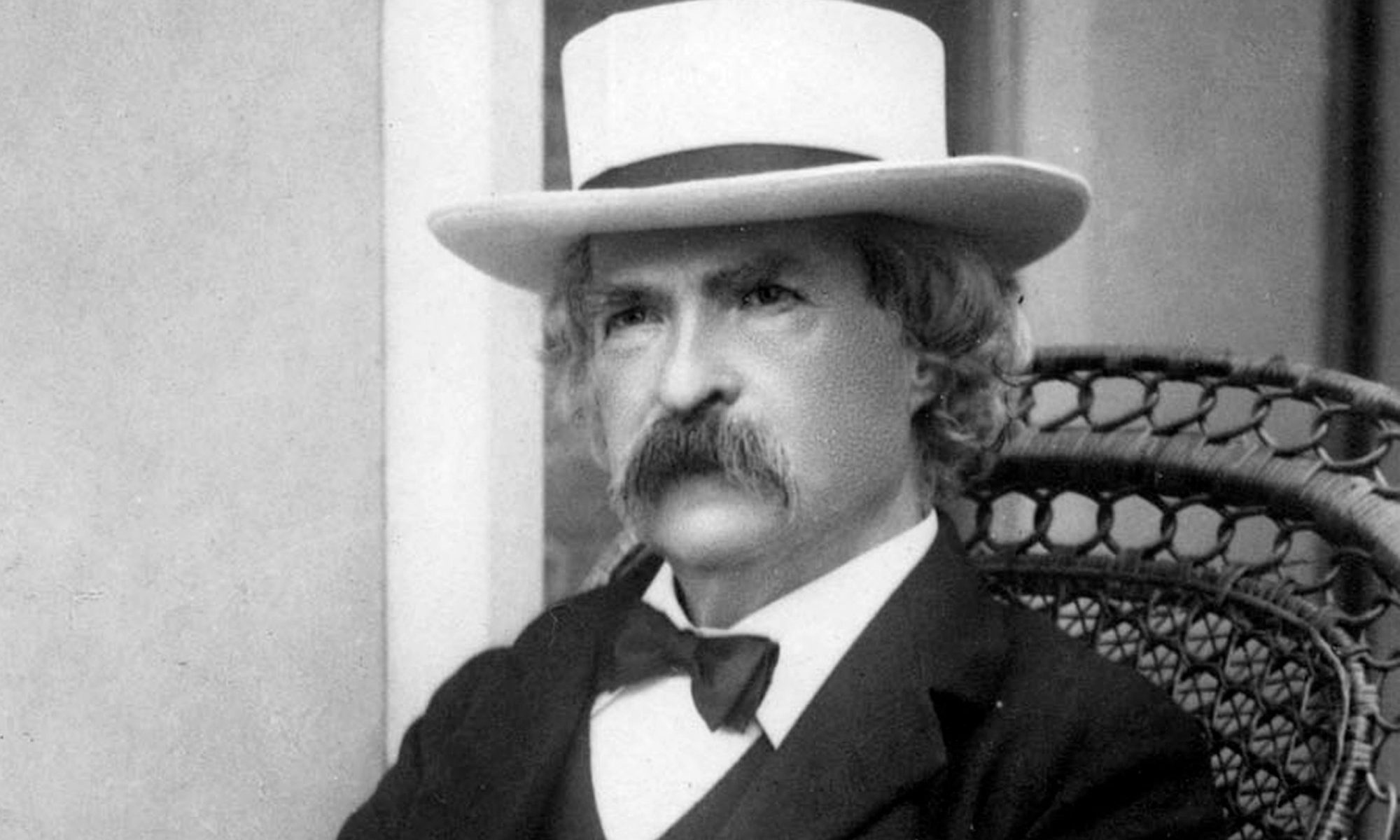
Mark Twain
“Sometimes I wonder whether the world is being run by smart people who are putting us on or by imbeciles who really mean it.”
Our Sun
The planets in our Solar System rotate, but does the Sun rotate?
Over, But Not Out
The term 10-4, like many other codes, refers to a distinctive communication lingo adopted by users of Citizens’Band (CB) radio – primarily among truckers hauling freight in the United States throughout the 1970s and 80s.
The code 10-6 means I’m busy at the moment, but stand by and 10-13 is a request to get information about the weather and road conditions. When a CB radio message asks ‘what’s your 10-20?’ they are asking for your location – where are you?
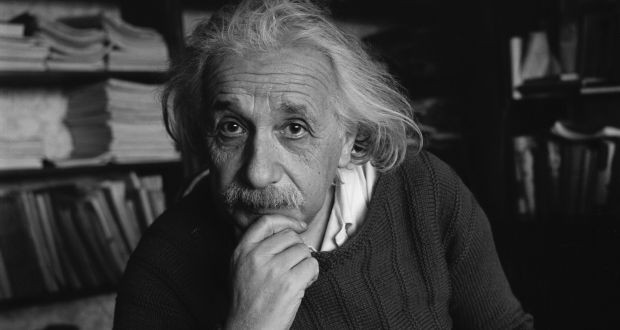
Albert Einstein
“Laws alone can not secure freedom of expression; in order that every man present his views without penalty there must be spirit of tolerance in the entire population.”
10-4
“10-4” is the common communication response acknowledging receipt of a message and signing off at the end of a radio transmission.
Do you know where it comes from or what 10-6 or 10-13 or 10-20 means?
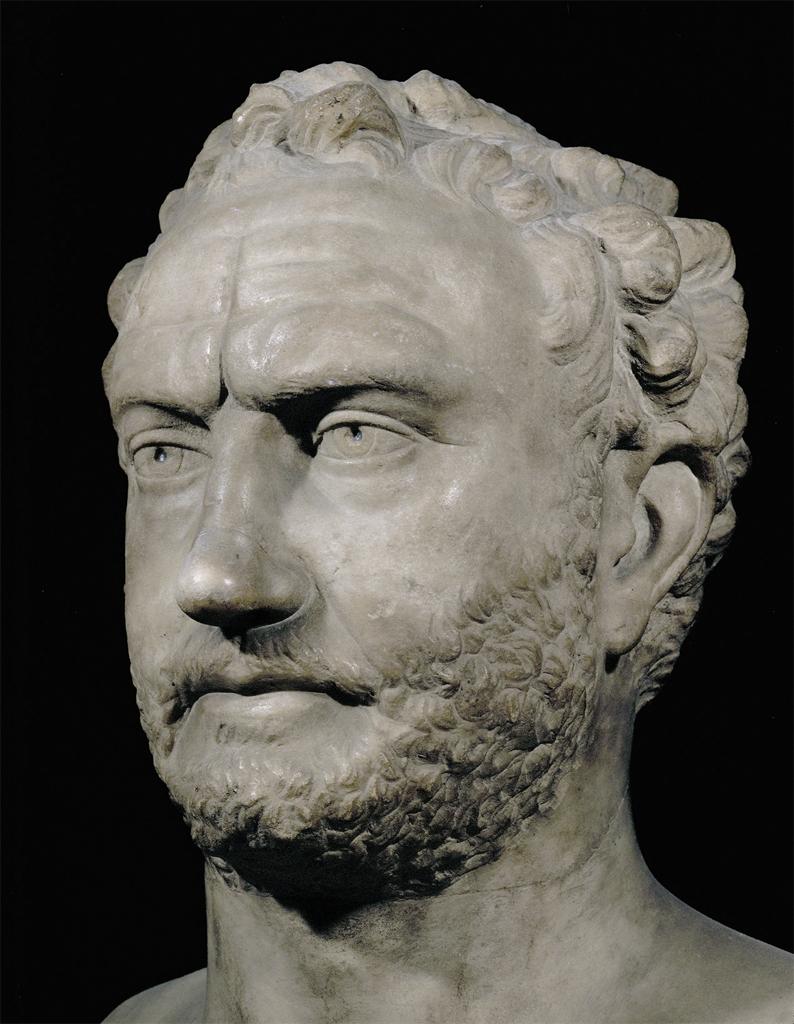
The First Historian
Thycydides is considered by many to be the first “true historian”, noted for using a fact-based scientific approach to recounting events, free of rumours and myths.
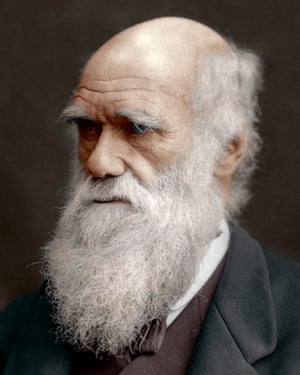
Charles Robert Darwin
“It is not the strongest of the species that survive, nor the most intelligent, but the ones most responsive to change.”